KeySure
PO Box 362 Hudson NY 12534-0362
http://www.keysure.net/ 1-518-828-5337
Some time ago we took responsibility for the protection of an apartment that contained several million dollars worth of art. The first thing we did was change the alarm codes, with re-keying of the locks scheduled for day two. At 3 a.m. the alarm went off, and the front door was discovered to be unlocked and open.
Upon re-keying the locks, one of our concerns became the keys that had to be, by law, left with the building. Traditionally, in most apartment buildings, the super puts a label on each set of keys and tosses them all into a drawer. Since the super’s office is generally less than fort- like, the keys are vulnerable, and it is easy for someone to take a key, rob an apartment, and then return the key.
 One approach commonly used is to put the keys in an envelope, seal it, and sign the back. This allows you to see whether the envelope has been opened. Unfortunately, envelopes are relatively fragile, and over time keys sometimes poke their way through.
One approach commonly used is to put the keys in an envelope, seal it, and sign the back. This allows you to see whether the envelope has been opened. Unfortunately, envelopes are relatively fragile, and over time keys sometimes poke their way through.
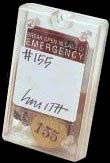
KEYController allows keys to be sealed in a small plastic box that can only be open by breaking, which removes all question as to whether the key has been accessed. Obviously, other things, like passwords, or access control cards, could just as easily be stored. And if neighbors give you keys to hold – particularly sensitive keys, like gun-lock keys – sealing them this way should give everyone a higher level of comfort: The keys are either there and sealed, or missing, or broken-into.
KeySure’s recommendation for setting up a system for a building is:
1. CODING: The KEYSURE system is based on a consecutive numbering system. Example: Numbering 1 through 100 if it is a 100 unit building. These numbers then become the code number for each apartment unit.
2. MASTER CODE LIST: Since most buildings have a computer print out tenant list or rent roll, we suggest you use this already existing list and simply consecutively number it. Exercise caution, and do not keep the list with the keys.
3. KEY TAGS: Each key will be put on a numbered key tag corresponding to the apartment code established above. Key tags are an integral part of the system and serve to organize and identify individual keys. The last thing you want, is to be seen trying keys in tenants doors to identify random keys.
4. APPLYING CODE NUMBER: Number the outside of the KEYController container with the same number that is on the key tag.
5. SIGNATURES: The tenant signs a signature on both inside surfaces where indicated. The signatures must be applied before the container is closed. The signatures on the inside insure the tenants Anonymity
6. CLOSING THE KEYController: After the signatures are applied and the key with tag is placed inside. close the container with a squeezing action, until a snap is heard. Caution: Once closed, the KEYController will have to be broken to gain access to the key.
7. MOTHER’S MAIDEN NAME: Have the tenant sign mother’s maiden name on the outside of the container. This will allow a tenant to check up on a key without breaking the container. It also serves to confuse anyone with criminal intent. [NOTE: Since this is a common measure used by banks and others, a middle name, or a pet’s name, could be used instead.]
8. STORAGE WALL CABINETS DRAWERS: Carefully load the containers keeping them in numerical order. Good order will make it that much easier to retrieve keys. Audit the key boxes on a scheduled basis to insure that they are all there and in order.
9. SECURITY POLICY: Security of any kind is only strengthened by having a well thought out written security policy. This written policy should be distributed to every tenant so that each tenant understands it and feels as though he or she is involved in the process of creating a more secure and safe environment.
We think the system is worth considering for your coop or condo, if you have concerns regarding the security of your keys. And for the storage of other items where you need to be able to confirm if they have been accessed.